Think about how much of the world relies on the internet. The government, military, academia, health care industry, and private industry not only collect, process, and store unprecedented amounts of data in cyberspace — they also rely on critical infrastructure systems in cyberspace to perform operations and deliver services.
An attack on this infrastructure could not only threaten customer data or a business’s bottom line — it could also threaten a nation’s security, economy, and public safety and health.
Considering its importance, I’ve compiled this guide on cybersecurity. Below, I’ll talk about what cybersecurity is exactly, how to protect your systems and data from attacks, and what resources to follow to stay up-to-date with emerging trends and technology related to cybersecurity news.
What is cybersecurity?
Cybersecurity is the practice of securing data, devices, programs, networks, and systems against attacks. These attacks, known as cyber attacks, are designed to exploit vulnerabilities in an individual’s device or enterprise’s system in order to disrupt, disable, destroy, or control their data or infrastructure.
Good cybersecurity involves multiple layers of protection across the data, devices, programs, networks, and systems of an enterprise. A combination of technology and best practices can provide an effective defense against the continually evolving and growing threats of cyberspace.
These threats include phishing, malware, ransomware, code injections, and more. The impact can vary depending on the scope of the attack. A cyber attack might result in the attacker making unauthorized purchases with an individual’s credit card info, or erasing an entire system after injecting malware into an organization’s code base.
While even the best cybersecurity can’t defend against every type or instance of attack, it can help to minimize the risks and impact of such attacks.
Types of Cybersecurity
Cybersecurity is a broad term that can be broken down into more specific subcategories. Below we’ll walk through five major types of cybersecurity.
Application Security
Application security, also known as AppSec, is the practice of developing, adding, and testing security features within web applications in order to protect them against attacks. Vulnerabilities, security misconfigurations, and design flaws can be exploited and result in malicious code injections, sensitive data exposure, system compromise, and other negative impacts.
AppSec is one of the most important types of cybersecurity because the application layer is the most vulnerable. According to Imperva research, nearly half of data breaches over the past several years originated at the web application layer.
Cloud Security
Cloud security is a relatively recent type of cybersecurity. It is the practice of protecting cloud computing environments as well as applications running in and data stored in the cloud.
Since cloud providers host third-party applications, services, and data on their servers, they have security protocols and features in place — but clients are also partially responsible and expected to configure their cloud service properly and use it safely.
Critical Infrastructure Security
Critical infrastructure security is the practice of protecting the critical infrastructure of a region or nation. This infrastructure includes both physical security and cyber networks, systems, and assets that provide physical and economic security or public health and safety. Think of a region’s electricity grid, hospitals, traffic lights, and water systems as examples.
Much of this infrastructure is digital or relies on the internet in some way to function. It is therefore susceptible to cyber attacks and must be secured.
Internet of Things (IoT) security
Internet of Things security, or IoT security, is the practice of protecting virtually any device that connects to the internet and can communicate with the network independently of human action. This includes baby monitors, printers, security cameras, motion sensors, and a billion other devices as well as the networks they’re connected to.
Since IoT devices collect and store personal information, like a person’s name, age, location, and health data, they can help malicious actors steal people’s identities and must be secured against unauthorized access and other threats.
Network Security
Network security is the practice of protecting computer networks and data against external and internal threats. Identity and access controls like firewalls, virtual private networks, and two-factor authentication can help.
Network security is typically broken down into three categories: physical, technical, and administrative. Each of these types of network security is about ensuring only the right people have access to network components (like routers), data that is stored in or transferred by the network, and the infrastructure of the network itself.
Cybersecurity Terms to Know
Cybersecurity is a very intimidating topic, not unlike cryptocurrency and artificial intelligence. It can be hard to understand, and, frankly, it sounds kind of ominous and complicated.
But fear not. We’re here to break this topic down into digestible pieces that you can rebuild into your own cybersecurity strategy. Bookmark this post to keep this handy glossary at your fingertips.
Here’s a comprehensive list of general cybersecurity terms you should know.
Authentication
Authentication is the process of verifying who you are. Your passwords authenticate that you really are the person who should have the corresponding username. When you show your ID (e.g., driver’s license, etc), the fact that your picture generally looks like you is a way of authenticating that the name, age, and address on the ID belong to you. Many organizations use two-factor authentication, which we cover later.
Backup
A backup refers to the process of transferring important data to a secure location like a cloud storage system or an external hard drive. Backups let you recover your systems to a healthy state in case of a cyber attack or system crash.
Behavior Monitoring
Behavior monitoring is the process of observing the activities of users and devices in your network to recognize any potential security events before they occur. Activities must not only be observed but also measured against baselines of normal behavior, trends, and organizational policies and rules.
For example, you might monitor and track when users log in and log out, if they request access to sensitive assets, and what websites they visit. Then say a user tries to log in at an unusual time, like the middle of the night. In that case, you could identify that as unusual behavior, investigate it as a potential security event, and ultimately block that log in attempt if you suspect an attack.
Bot
A bot, short for robot, is an application or script designed to perform automated and repetitive tasks. Some bots have legitimate purposes, like chatbots that answer commonly asked questions on a website. Others are used for malicious purposes, like sending spam emails or conducting DDoS attacks. As bots become more sophisticated, it gets harder to tell the difference between good bots and bad bots or even bots from human users. That’s why bots pose an ever-growing threat to many individuals and organizations.
CIA Triad
The CIA triad is a model that can be used to develop or evaluate an organization’s cybersecurity systems and policies.
The CIA triad refers to confidentiality, integrity, and availability. In practice, this model ensures data is disclosed only to authorized users, remains accurate and trustworthy throughout its lifecycle, and can be accessed by authorized users when needed in spite of software failures, human error, and other threats.

Data Breach
A data breach refers to the moment a hacker gains unauthorized entry or access to a company’s or an individual’s data.
Digital Certificate
A digital certificate, also known as an identity certificate or public key certificate, is a type of passcode used to securely exchange data over the internet. It’s essentially a digital file embedded in a device or piece of hardware that provides authentication when it sends and receives data to and from another device or server.
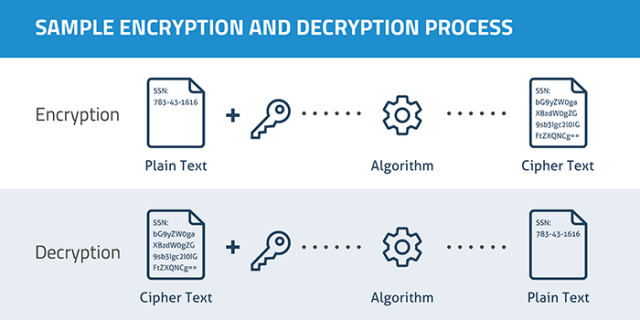
Encryption
Encryption is the practice of using codes and ciphers to encrypt data. When data is encrypted, a computer uses a key to turn the data into unintelligible gibberish. Only a recipient with the correct key is able to decrypt the data. If an attacker gets access to strongly encrypted data but doesn’t have the key, they aren’t able to see the unencrypted version.
HTTP and HTTPS
Hypertext Transfer Protocol (HTTP) is how web browsers communicate. You’ll probably see an http:// or https:// in front of the websites you visit. HTTP and HTTPS are the same, except HTTPS encrypts all data sent between you and the web server — hence the “S” for security. Today, nearly all websites use HTTPS to improve the privacy of your data like the free SSL provided by the free Content Hub.
Vulnerability
A vulnerability is a place of weakness that a hacker might exploit when launching a cyber attack. Vulnerabilities might be software bugs that need to be patched, or a password reset process that can be triggered by unauthorized people. Defensive cybersecurity measures (like the ones we talk about later) help ensure data is protected by putting layers of protections between attackers and the things they’re trying to do or access.
Types of Cyber Attacks
- Password Guessing Attack
- Distributed Denial of Service (DDoS) Attack
- Malware Attack
- Phishing Attack
- Man-in-the-Middle (MitM) Attack
- Cross Site Scripting Attack
- SQL Injection Attack
A cyber attack is a deliberate and typically malicious intent to capture, modify, or erase private data. Cyber attacks are committed by external security hackers and, sometimes, unintentionally by compromised users or employees. These cyber attacks are committed for a variety of reasons. Some are looking for ransom, while some are simply launched for fun.
Below we’ll briefly go over the most common cyber threats.
1. Password Guessing (Brute Force) Attack
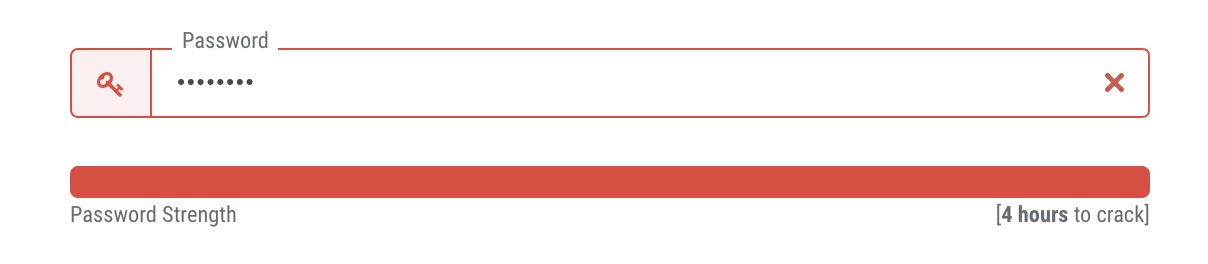
A password guessing (or “credential stuffing”) attack is when an attacker continually attempts to guess usernames and passwords. This attack will often use known username and password combinations from past data breaches.
An attacker is successful when people use weak passwords or use the password between different systems (e.g., when your Facebook and Twitter password are the same, etc). Your best defense against this kind of attack is using strong passwords and avoiding using the same password in multiple places as well as using two factor authentication, as we talk about later.)
2. Distributed Denial of Service (DDoS) Attack
A distributed denial of service (DDoS) attack is when a hacker floods a network or system with a ton of activity (such as messages, requests, or web traffic) in order to paralyze it.
This is typically done using botnets, which are groups of internet-connected devices (e.g., laptops, light bulbs, game consoles, servers, etc) infected by viruses that allow a hacker to harness them into performing many kinds of attacks.

3. Malware Attack
Malware refers to all types of malicious software used by hackers to infiltrate computers and networks and collect susceptible private data. Types of malware include:
- Keyloggers, which track everything a person types on their keyboard. Keyloggers are usually used to capture passwords and other private information, such as social security numbers.
- Ransomware, which encrypts data and holds it hostage, forcing users to pay a ransom in order to unlock and regain access to their data.
- Spyware, which monitors and “spies” on user activity on behalf of a hacker.
Furthermore, malware can be delivered via:
- Trojan horses, which infect computers through a seemingly benign entry point, often disguised as a legitimate application or other piece of software.
- Viruses, which corrupt, erase, modify, or capture data and, at times, physically damage computers. Viruses can spread from computer to computer, including when they are unintentionally installed by compromised users.
- Worms, which are designed to self-replicate and autonomously spread through all connected computers that are susceptible to the same vulnerabilities. .
4. Phishing Attack
A phishing attack is when hackers try to trick people into doing something. Phishing scams can be delivered through a seemingly legitimate download, link, or message.
It’s a very common type of cyber attack — 57% of respondents in a third-party survey said their organization experienced a successful phishing attack in 2020, up from 55% in 2019. And the impact of successful phishing attacks range from loss of data to financial loss.
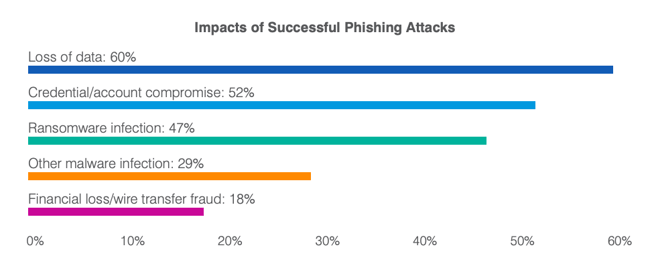
Phishing is typically done over email or through a fake website; it’s also known as spoofing. Additionally, spear phishing refers to when a hacker focuses on attacking a particular person or company, such as stealing their identity, instead of creating more general-purpose spams.
5. Man-in-the-Middle (MitM) Attack
A Man-in-the-Middle (MitM) attack is when an attacker intercepts communications or transactions between two parties and inserts themselves in the middle. The attacker can then intercept, manipulate, and steal data before it reaches its legitimate destination. For example, say a visitor is using a device on public WiFi that hasn’t been secured properly, or at all. An attacker could exploit this vulnerability and insert themselves between the visitor’s device and the network to intercept login credentials, payment card information, and more.
This type of cyber attack is so successful because the victim has no idea that there is a “man in the middle.” It just seems like they’re browsing the web, logging into their bank app, and so on.
%20Attack-p-500.jpeg?width=650&name=605cab5ff8f386ea033ae16c_Man-in-the-Middle)%20Attack-p-500.jpeg)
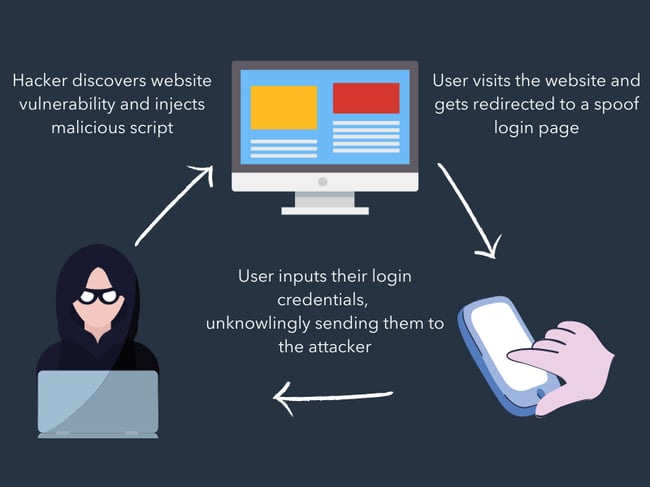
6. Cross Site Scripting Attack
A cross site scripting attack, or XSS attack, is when an attacker injects malicious code into an otherwise legitimate website or application in order to execute that malicious code in another user’s web browser.
Because that browser thinks the code is coming from a trusted source, it will execute the code and forward information to the attacker. This information might be a session token or cookie, login credentials, or other personal data.
Here’s an illustrated example of an XSS attack:
7. SQL Injection Attack
An SQL injection attack is when an attacker submits malicious code through an unprotected form or search box in order to gain the ability to view and modify the website’s database. The attacker might use SQL, short for Structured Query Language, to make new accounts on your site, add unauthorized links and content, and edit or delete data.
This is a common WordPress security issue since SQL is the preferred language on WordPress for database management.
Cybersecurity Best Practices: How to Secure Your Data
Cybersecurity can’t be boiled down into a 1-2-3-step process. Securing your data involves a mix of best practices and defensive cybersecurity techniques. Dedicating time and resources to both is the best way to secure your — and your customers’ — data.
Defensive Cybersecurity Solutions
All businesses should invest in preventative cybersecurity solutions. Implementing these systems and adopting good cybersecurity habits (which we discuss next) will protect your network and computers from outside threats.
Here’s a list of five defensive cybersecurity systems and software options that can prevent cyber attacks — and the inevitable headache that follows. Consider combining these solutions to cover all your digital bases.
Antivirus Software
Antivirus software is the digital equivalent of taking that vitamin C boost during flu season. It’s a preventative measure that monitors for bugs. The job of antivirus software is to detect viruses on your computer and remove them, much like vitamin C does when bad things enter your immune system. (Spoken like a true medical professional …) Antivirus software also alerts you to potentially unsafe web pages and software.
Learn more: McAfee, Norton. or Panda (for free)
Firewall
A firewall is a digital wall that keeps malicious users and software out of your computer. It uses a filter that assesses the safety and legitimacy of everything that wants to enter your computer; it’s like an invisible judge that sits between you and the internet. Firewalls are both software and hardware-based.
Learn more: McAfee LiveSafe or Kaspersky Internet Security
Invest in Threat Detection and Prevention
Whether you’re using the Content Hub or a common website hosting service like WordPress, it’s essential to integrate a tool to scan and detect threats. Most content management systems will include a malware scanning and threat detection feature within the platform. But if you use platforms like WordPress, you should invest in a security scanner.
Single Sign-On (SSO)
Single sign-on (SSO) is a centralized authentication service through which one login is used to access an entire platform of accounts and software. If you’ve ever used your Google account to sign up or into an account, you’ve used SSO. Enterprises and corporations use SSO to allow employees access to internal applications that contain proprietary data.
Learn more: Okta or LastPass
Two-Factor Authentication (2FA)
Two-factor authentication (2FA) is a login process that requires a username or pin number and access to an external device or account, such as an email address, phone number, or security software. 2FA requires users to confirm their identity through both and, because of that, is far more secure than single factor authentication.
Learn more: Duo
Virtual Private Network (VPN)
A virtual private network (VPN) creates a “tunnel” through which your data travels when entering and exiting a web server. That tunnel encrypts and protects your data so that it can’t be read (or spied on) by hackers or malicious software. While secure VPNs protect against spyware, they can’t prevent viruses from entering your computer through seemingly legitimate channels, like phishing or even a fake VPN link. Because of this, VPNs should be combined with other defensive cybersecurity measures in order to protect your data.
Learn more: Cisco’s AnyConnect or Palo Alto Networks’ GlobalProtect
Cybersecurity Tips for Business
Defensive cybersecurity solutions won’t work unless you do. To ensure your business and customer data is protected, adopt these good cybersecurity habits across your organization.
Require strong credentials.
Require both your employees and users (if applicable) to create strong passwords. This can be done by implementing a character minimum as well as requiring a mix of upper and lowercase letters, numbers, and symbols. More complicated passwords are harder to guess by both individuals and bots. Also, require that passwords be changed regularly.
Control and monitor employee activity.
Within your business, only give access to important data to authorized employees who need it for their job. Prohibit data from sharing outside the organization, require permission for external software downloads, and encourage employees to lock their computers and accounts whenever not in use.
Know your network.
With the rise of the Internet of Things, IoT devices are popping up on company networks like crazy. These devices, which are not under company management, can introduce risk as they’re often unsecured and run vulnerable software that can be exploited by hackers and provide a direct pathway into an internal network.
“Make sure you have visibility into all the IoT devices on your network. Everything on your corporate network should be identified, properly categorized, and controlled. By knowing what devices are on your network, controlling how they connect to it, and monitoring them for suspicious activities, you’ll drastically reduce the landscape attackers are playing on.” — Nick Duda, Principal Security Officer at HubSpot
Read about how HubSpot gains device visibility and automates security management in this case study compiled by security software ForeScout.
Download patches and updates regularly.
Software vendors regularly release updates that address and fix vulnerabilities. Keep your software safe by updating it on a consistent basis. Consider configuring your software to update automatically so you never forget.
Make it easy for employees to escalate issues.
If your employee comes across a phishing email or compromised web page, you want to know immediately. Set up a system for receiving these issues from employees by dedicating an inbox to these notifications or creating a form that people can fill out.
Cybersecurity Tips for Individuals
Cyber threats can affect you as an individual consumer and internet user, too. Adopt these good habits to protect your personal data and avoid cyber attacks.
Mix up your passwords.
Using the same password for all your important accounts is the digital equivalent of leaving a spare key under your front doormat. A recent study found that over 80% of data breaches were a result of weak or stolen passwords. Even if a business or software account doesn’t require a strong password, always choose one that has a mix of letters, numbers, and symbols and change it regularly.
Monitor your bank accounts and credit frequently.
Review your statements, credit reports, and other critical data on a regular basis and report any suspicious activity. Additionally, only release your social security number when absolutely necessary.
Be intentional online.
Keep an eye out for phishing emails or illegitimate downloads. If a link or website looks fishy (ha — get it?), it probably is. Look for bad spelling and grammar, suspicious URLs, and mismatched email addresses. Lastly, download antivirus and security software to alert you of potential and known malware sources.
Back up your data regularly.
This habit is good for businesses and individuals to master — data can be compromised for both parties. Consider backups on both cloud and physical locations, such as a hard drive or thumb drive.
Why You Should Care About Cybersecurity
According to a report by RiskBased Security, there were 3,932 data breaches reported in 2020, which exposed over 37 billion records. Moreover, a recent study found that the global average cost of a data breach amounted to 3.86 million U.S. dollars in 2020. That means the cost of data breaches amounted to approximately 15.2 billion dollars last year.
Small to medium-sized businesses (SMBs) are especially at risk. You might see corporations like Target and Sears topping the headlines as top data breach victims, but it’s actually SMBs that hackers prefer to target.
Why? They have more — and more valuable — digital assets than your average consumer but less security than a larger enterprise-level company … placing them right in a “hackers’ cybersecurity sweet spot.”
Security breaches are frustrating and frightening for both businesses and consumers. In a survey by Measure Protocol, approximately 86% of respondents said that recent privacy breaches in the news had impacted their willingness to share personal information to some extent.
But cybersecurity is about more than just avoiding a PR nightmare. Investing in cybersecurity builds trust with your customers. It encourages transparency and reduces friction as customers become advocates for your brand.
“Everyone has a role in helping to protect customers’ data. Here at HubSpot, every employee is empowered to solve for customer needs in a safe and secure way. We want to harness everyone’s energy to provide a platform that customers trust to correctly and safely store their data.” — Chris McLellan, HubSpot Chief Security Officer
Keep your business ahead of the tech curve with the tips, systems & recommended resources in our guide to staying current on emerging tech.
Cybersecurity Resources
The resources below will help you learn more about cybersecurity and how to better equip your business and team. We also recommend checking out the most popular cybersecurity podcasts and cybersecurity blogs, too.
National Institute of Standards and Technology (NIST)
NIST is a government agency that promotes excellence in science and industry. It also contains a Cybersecurity department and routinely publishes guides that standards.
Bookmark: The Computer Security Resource Center (CSRC) for security best practices, called NIST Special Publications (SPs).
The Center for Internet Security (CIS)
CIS is a global, non-profit security resource and IT community used and trusted by experts in the field.
Bookmark: The CIS Top 20 Critical Security Controls, which is a prioritized set of best practices created to stop the most pervasive and dangerous threats of today. It was developed by leading security experts from around the world and is refined and validated every year.
Cybrary
Cybrary is an online cybersecurity education resource. It offers mostly free, full-length educational videos, certifications, and more for all kinds of cybersecurity topics and specializations.
Bookmark: The Certified Information Systems Security Professional (CISSP) 2021, which is the most recent course for information security professionals. Earning this “gold standard” of cybersecurity certifications will set you apart from other information security professionals.
The Cyber Readiness Institute
The Cyber Readiness Institute is an initiative that convenes business leaders from different sectors and regions to share resources and knowledge to ultimately advance the cyber readiness of small and medium-sized businesses.
Bookmark: The Cyber Readiness Program, which is a free, online program designed to help small and medium-sized enterprises secure their data, employees, vendors, and customers against today’s most common cyber vulnerabilities.
Signing Off … Securely
Cyber attacks may be intimidating, but cybersecurity as a topic doesn’t have to be. It’s imperative to be prepared and armed, especially if you’re handling others’ data. Businesses should dedicate time and resources to protecting their computers, servers, networks, and software and should stay up-to-date with emerging tech.
Handling data with care only makes your business more trustworthy and transparent — and your customers more loyal.
Note: Any legal information in this content is not the same as legal advice, where an attorney applies the law to your specific circumstances, so we insist that you consult an attorney if you’d like advice on your interpretation of this information or its accuracy. In a nutshell, you may not rely on this as legal advice or as a recommendation of any particular legal understanding.
The Leading Source of Insights On Business Model Strategy & Tech Business Models
Cybersecurity In A Nutshell And Why It Matters In Business
Business / By Gennaro Cuofano / May 21, 2024
Cybersecurity refers to the practice of implementing defense programs against cyber threats, exploits, and attacks. It aims to secure computers, servers, mobile devices, electronic systems, networks, and data from malicious attacks. Simply put, cybersecurity serves as the security unit of the entire cyberspace.
| Aspect | Explanation |
|---|---|
| Definition | Cybersecurity, often abbreviated as “InfoSec” (Information Security), is the practice of protecting computer systems, networks, and digital data from theft, damage, or unauthorized access. It encompasses a wide range of technologies, processes, and practices designed to safeguard information and ensure the confidentiality, integrity, and availability of digital assets. Cybersecurity is essential in an increasingly digital and interconnected world to counteract cyber threats and attacks. |
| Key Concepts | – Confidentiality: Ensuring that sensitive data is only accessible to authorized individuals or systems. – Integrity: Maintaining the accuracy and trustworthiness of data and systems by preventing unauthorized alterations. – Availability: Ensuring that information and systems are accessible when needed and not subject to disruption or downtime. – Authentication: Verifying the identity of users or systems to prevent unauthorized access. – Authorization: Granting appropriate permissions and access rights to authorized users. – Vulnerabilities: Weaknesses in systems or software that can be exploited by attackers. – Threats: Potential dangers or harmful events that can exploit vulnerabilities. – Malware: Malicious software designed to harm or gain unauthorized access. – Firewalls: Network security devices that monitor and control incoming and outgoing traffic. – Intrusion Detection: Systems that identify and respond to unauthorized access or security breaches. – Encryption: The process of encoding data to protect it from unauthorized access. – Incident Response: Procedures and plans to address and mitigate cybersecurity incidents. |
| Characteristics | – Continuous Evolution: Cybersecurity is an ongoing process that evolves alongside technology and emerging threats. – Interdisciplinary: It draws from computer science, risk management, law, and ethics. – Risk-Based Approach: Prioritizing security measures based on potential risks and vulnerabilities. – Global Scope: Cybersecurity is a global concern, with international implications and challenges. – Compliance Requirements: Many industries and organizations have legal and regulatory requirements related to cybersecurity. |
| Implications | – Data Breaches: Cybersecurity failures can lead to data breaches, exposing sensitive information. – Financial Loss: Organizations can suffer financial losses due to cyberattacks, including theft, ransom payments, and litigation costs. – Reputation Damage: Security incidents can damage an organization’s reputation and erode customer trust. – Legal Consequences: Non-compliance with cybersecurity regulations can result in legal and regulatory penalties. – National Security: Cybersecurity is critical for national security, protecting government systems and infrastructure. – Innovation: Balancing security with the need for innovation and digital transformation is a constant challenge. |
| Advantages | – Protection: Effective cybersecurity measures protect sensitive data and systems from unauthorized access. – Risk Reduction: It reduces the risk of financial losses, data breaches, and reputation damage. – Compliance: Meeting cybersecurity requirements and standards helps organizations avoid legal and regulatory consequences. – Confidence: It instills confidence in customers, partners, and stakeholders. – National Security: Cybersecurity safeguards critical infrastructure and national interests. |
| Drawbacks | – Complexity: Cybersecurity measures can be complex and costly to implement and maintain. – False Positives: Security systems may generate false alarms or block legitimate actions. – Resource Constraints: Smaller organizations may lack the resources to invest in robust cybersecurity. – Human Error: Even with strong security measures, human error can introduce vulnerabilities. – Adaptability: Cyber attackers continually evolve their tactics, requiring constant adaptation of defenses. |
| Applications | – Enterprise Security: Protecting an organization’s digital assets, including networks, data centers, and endpoints. – Cloud Security: Ensuring the security of data and applications hosted in cloud environments. – Mobile Security: Safeguarding mobile devices and applications from threats. – Critical Infrastructure: Protecting essential services such as energy, transportation, and healthcare. – Government and Military: National security and defense rely heavily on cybersecurity. – Consumer Devices: Ensuring the security of personal devices and IoT (Internet of Things) devices. |
| Use Cases | – Antivirus Software: Detects and removes malware from computers and networks. – Firewalls: Control network traffic to prevent unauthorized access. – Multi-Factor Authentication (MFA): Requires multiple forms of verification to access accounts or systems. – Penetration Testing: Ethical hacking to identify vulnerabilities in systems. – Security Information and Event Management (SIEM): Real-time monitoring and analysis of security events. – Encryption: Protects data during transmission and storage. – Incident Response Plans: Defined procedures for responding to security incidents. |
| Future Trends | – AI and Machine Learning: AI-powered cybersecurity tools for threat detection and response. – Zero Trust Security: The principle of “trust no one” and continuously verifying access. – IoT Security: Growing concerns around securing the Internet of Things devices. – Quantum-Safe Cryptography: Preparing for future threats posed by quantum computing. – Cybersecurity Regulations: Increasing regulatory requirements for data protection. |
- Defining Cybersecurity
- Why is Cybersecurity Important?
- Demand in Cybersecurity
- How Businesses Benefit From Cybersecurity
- Key Highlights
- Related Business Frameworks
Defining Cybersecurity
The recent advancement of technologies has brought an immense need for more refined programs against cyber threats.
For a single user alone, cyber-attacks can jeopardize one’s identity or even become subject to extortion.
These threats should be regarded seriously since they affect you and those you love.
As for businesses, once their data is compromised, all their hard work goes down the drain.
Depending on the nature of the threat, your reputation could also be jeopardized, making it even more difficult for you to recover.
For these reasons, a highly secured infrastructure, including power plants, hospitals, software, and systems, have to be protected.
Furthermore, cybersecurity plays a fundamental role in keeping society in harmony.
Servers are considered secured if multiple layers of security protocols get spread out across the systems.
The such protocol also includes computers, networks, data, and programs surrounding a single server.
When maintaining an organization’s safety, true cybersecurity is a triad between its people, technology, and methodology.
A reliable defense mechanism should complement one another to shield against potential cyber-attacks.
This unification is also helpful in augmenting uniform security operation functions.
Why is Cybersecurity Important?
Every organization much observe a comprehensive cybersecurity protocol to resolve issues before they get out of hand.
Cyber threats continue to rise globally, making it imperative to look for potential danger.
Reports even revealed that there were 7.9 billion records breached during the first nine months of 2019 alone.
This figure continues to rise as technological advancements progress throughout the world.
According to recent data, healthcare, retail, and public businesses are likely victims of such cyber exploitations.
These malicious attacks often stem from individuals looking to collect financial and medical data.
The information collected is then targeted for customer data, corporate espionage, or customer attacks.
Demand in Cybersecurity
The increasing cyber threats against organizations have led entrepreneurs to seek ways to protect themselves from attackers.
Governments worldwide also noticed and established methods to help businesses implement cyber-security practices.
For example, the US National Institute of Standards and Technology (NIST) introduced its cybersecurity framework.
Their goal is to fight against the proliferation of malicious code and detect threats early on.
Through routine monitoring performed in real-time, all electronic resources get tracked at all times.
As a result, the labor market expected demand for technical cybersecurity skills.
The US Bureau of Labor Statistics findings shows that there can be a 32% growth in cybersecurity-related roles by 2028.
Technological advancements, data, and privacy concerns are some of the issues that can only be resolved by cybersecurity specialists and experts.
Cybersecurity experts play a huge role in cyber law, and data protection compliance with legislation.
Apart from gaining a deep understanding of cybersecurity technology, they are well-informed of the policies mandated by law.
Thus, it is their responsibility to look for ways to organize data processes, ensure protection, and maintain compliance.
How Businesses Benefit From Cybersecurity
Although technology brings us countless opportunities to make our lives easier, the constant connectivity with the digital world brings us closer to many vulnerabilities.
Both businesses and their customers immerse themselves with faster, smarter, and more efficient technologies.
There can be cyber threats from smartphones, applications, and home appliances to automotive vehicles unless we are heavily secured.
Emerging businesses relatively new in the industry have also overlooked carrying out property security measures against cyber threats.
As a result, the pioneering enterprises prioritizing cybersecurity maintain the position of leaders. Coming entrepreneurs must understand that establishing a good product is not enough.
To succeed, you must withstand the vulnerabilities, risks, and dangers of launching your brand.
Furthermore, enterprises, whether big or small, must recognize the importance of cybersecurity.
These protection layers will always come through during hacks, abuse, exploitation of private data, and a risk-laden future.
Build Your Reputation as a Brand
Apart from launching the product that will lead your business to success, you have to prepare for the potential risks that come with it.
Implementing cybersecurity frameworks might have substantial costs, but it offers numerous benefits.
When your customers know your website is safe, they won’t hesitate to drive your brand’s traffic.
Consider the conversion opportunities you may lose if your target market finds your page unsafe.
Research reveals that approximately 40% of online shoppers won’t make a purchase soon after they realize your website is not secured.
This finding should not be a surprise now that more consumers are well-informed about data privacy and security.
Safeguard Sensitive Data
The most apparent advantage of cybersecurity is the safeguarding of your sensitive data.
This safeguard is especially crucial for organizations that manage a large data set involving private customer information.
Once they are leaked, the business and its customers are in danger.
Improve SEO Rankings
If you are just starting with your business, SEO can help increase your brand awareness. Search Engine Optimization determines how your webpage ranks within search engines.
The more you appear on relevant searches, the more people can discover your business.
As the pillar of digital marketing, organizations ensure that their website complies with SEO standards. It provides companies with organic traffic as well as lead opportunities.
Popular search engines like Google prioritize quality user experience when formulating rankings of landing pages.
After all, their reputation can be on the line if they lure searchers into untrusted websites that offer irrelevant content.
Moreover, they reinforce cybersecurity through the HyperText Transfer Protocol Secure HTTPS.
One of the primary requirements of search engines in SEO rankings is to require websites to utilize HTTPS.
HTTPS provides sufficient encryption on confidential information like credit card numbers, passwords, and usernames while they are processed on a site.
For websites with no HTTPS, the browser would promptly warn the users of the risks of disclosing personal information.
Reduce Downtime
A vital benefit of cybersecurity is minimizing the downtime of your website. Any business would prefer to reduce as much downtime as possible to prevent losses.
The tiniest amount of time lost trying to recover from cyber attacks is equivalent to profit missed.
Business websites are commonly affected by Distributed Denial of Service or DDoS attacks.
It is when a hacker would leverage a network of infected systems to spam servers with malicious traffic. As a result, organic traffic will be denied access to the website affected.
Presently, cybersecurity practices offer DDoS attack mitigation to prevent such events. Experts can also implement a web application firewall to prevent these cyber threats.
Key Highlights
- Definition of Cybersecurity:
- Cybersecurity is the practice of defending against cyber threats, attacks, and exploits.
- It aims to secure computers, networks, devices, data, and electronic systems from malicious activities.
- Importance of Cybersecurity:
- Cyber threats can lead to identity theft, extortion, and other harmful consequences for individuals.
- Businesses can suffer data breaches, resulting in reputation damage and loss of hard work.
- Essential infrastructure like power plants and hospitals must be protected from cyber threats.
- Cybersecurity plays a vital role in maintaining societal harmony.
- Elements of Cybersecurity:
- Effective cybersecurity involves a combination of people, technology, and methodology.
- A secure infrastructure includes multiple layers of security protocols across systems, including servers, computers, networks, data, and programs.
- Growing Cyber Threats:
- Cyber threats are increasing globally, with reports of billions of records breached.
- Industries like healthcare, retail, and public businesses are common targets for cyber attacks.
- Attackers often seek financial and medical data for various malicious purposes.
- Demand for Cybersecurity:
- Rising cyber threats have led to a demand for cybersecurity skills.
- Organizations and governments are implementing cybersecurity practices to counter malicious activities.
- Cybersecurity experts play a role in cyber law, data protection compliance, and maintaining security policies.
- Business Benefits of Cybersecurity:
- Constant connectivity increases vulnerabilities, making cybersecurity crucial.
- Prioritizing cybersecurity enhances a brand’s reputation and leadership position.
- Safeguarding sensitive data is a key advantage of cybersecurity.
- SEO and Cybersecurity:
- Implementing cybersecurity measures can improve SEO rankings.
- Search engines prioritize secure websites (HTTPS) for user experience and data protection.
- Reducing Downtime:
- Cybersecurity minimizes downtime caused by cyber attacks.
- DDoS attacks are a common threat, but mitigation techniques and web application firewalls can prevent them.
| Related Frameworks, Concepts, Models | Description | When to Apply |
|---|---|---|
| Defense in Depth | – A multi-layered approach to security, where multiple defenses are placed throughout an IT system. | – Apply to increase security by ensuring that if one layer fails, others will still be in place to prevent a breach. |
| Zero Trust Architecture | – A security model that assumes no user or device, inside or outside the network, should be trusted by default. | – Implement when aiming to reduce the risk of internal and external threats. – Ideal for cloud-based environments. |
| Incident Response Plan (IRP) | – A set of procedures for detecting, responding to, and recovering from security incidents. | – Use to prepare for potential security breaches and ensure a quick and effective response. |
| Risk Assessment | – The process of identifying, evaluating, and prioritizing risks to an organization’s IT infrastructure. | – Apply to understand and mitigate potential risks. – Essential for developing a comprehensive cybersecurity strategy. |
| Encryption | – The method of converting information or data into a code to prevent unauthorized access. | – Use to protect sensitive data both in transit and at rest. – Crucial for compliance with data protection regulations. |
| Firewall | – A network security device that monitors and controls incoming and outgoing network traffic based on predetermined security rules. | – Apply to create a barrier between a trusted internal network and untrusted external networks. |
| Intrusion Detection System (IDS) | – A device or software application that monitors network or system activities for malicious activities or policy violations. | – Use to detect and respond to potential threats in real-time. |
| Security Information and Event Management (SIEM) | – A solution that provides real-time analysis of security alerts generated by applications and network hardware. | – Implement for comprehensive monitoring, event correlation, and incident management. |
| Multi-Factor Authentication (MFA) | – A security system that requires multiple methods of authentication from independent categories of credentials. | – Apply to enhance security by adding an extra layer of protection beyond just passwords. |
| Vulnerability Assessment | – The process of identifying, quantifying, and prioritizing vulnerabilities in a system. | – Use to proactively identify and address weaknesses in IT systems and networks. |
Read Next: Cloud Business Models, IaaS, PaaS, SaaS, AI Economy, C3.ai Business Model, Enterprise AI Business Model.
Main Guides:
- Business Models
- Business Strategy
- Marketing Strategy
- Business Model Innovation
- Platform Business Models
- Network Effects In A Nutshell
- Digital Business Models
Related Business Frameworks
Related
NIST Cybersecurity Framework
The NIST Cybersecurity Framework was developed in response to a growing awareness of cybersecurity risks and the need for a standardized approach to managing those risks. It was first published in 2014, following an executive order aimed at improving the cybersecurity of critical infrastructure in the United States. The Framework…
Vulnerability Scanning
Vulnerability scanning is a critical component of proactive cybersecurity, aimed at identifying and mitigating security vulnerabilities in an organization’s IT infrastructure and systems. By systematically scanning networks, applications, and devices for known vulnerabilities, organizations can identify potential entry points for cyberattacks and prioritize remediation efforts to strengthen their security posture.…
More Resources
- NIST Cybersecurity Framework
- Blockchain In A Nutshell And Why It Matters In Business
- Ad-Ops In A Nutshell And Why It Matters In Business
- Business Logic Layer And Why It Matters To…
- What Is Business Acumen And Why It Matters In Business
- Agile Business Analysis And Why It Matters In Business
- What Is Business Ethics And Why It Matters In Business
- What Is A Business Plan And Why It Matters In Business